A Visual Guide to the Howey Test
Disclaimer: I am not a lawyer, and I am not your lawyer.
I have been in an uncountable number of conversations over the past few years discussing the question of what defines a “security” in the context of cryptocurrencies, cryptonetworks, and token offerings.
Here is my current understanding, including a number of key questions I am still working on. I invite any and all corrections to this visual framework. And I should note that this is a high-level framework: the nuanced details are the subject of many enforcements, settlements, and litigations and will be worked out over a long-period of time to come.
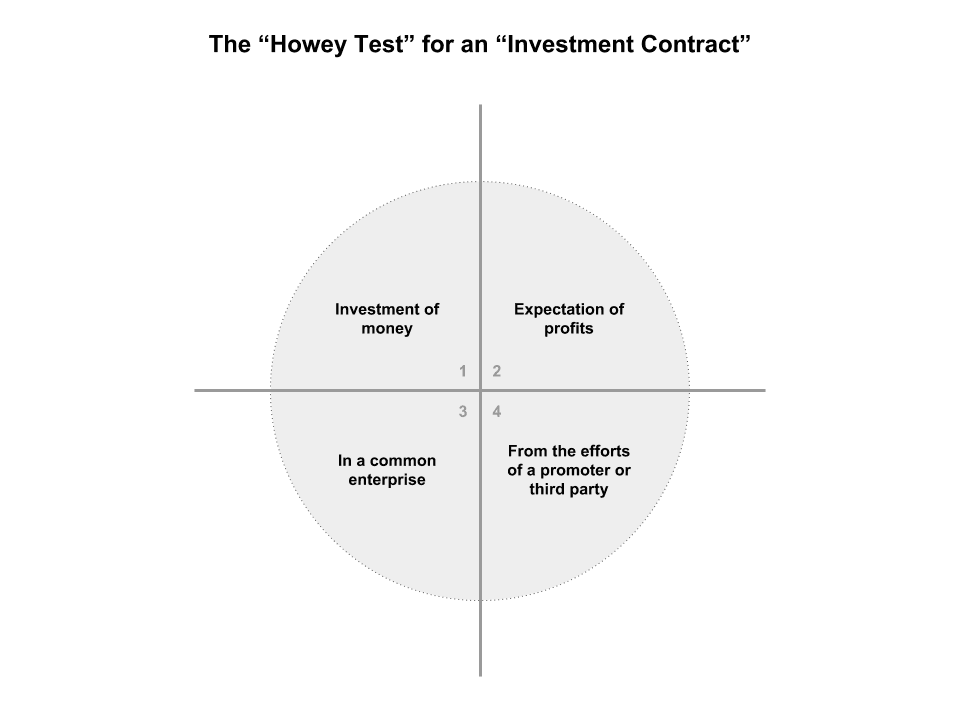
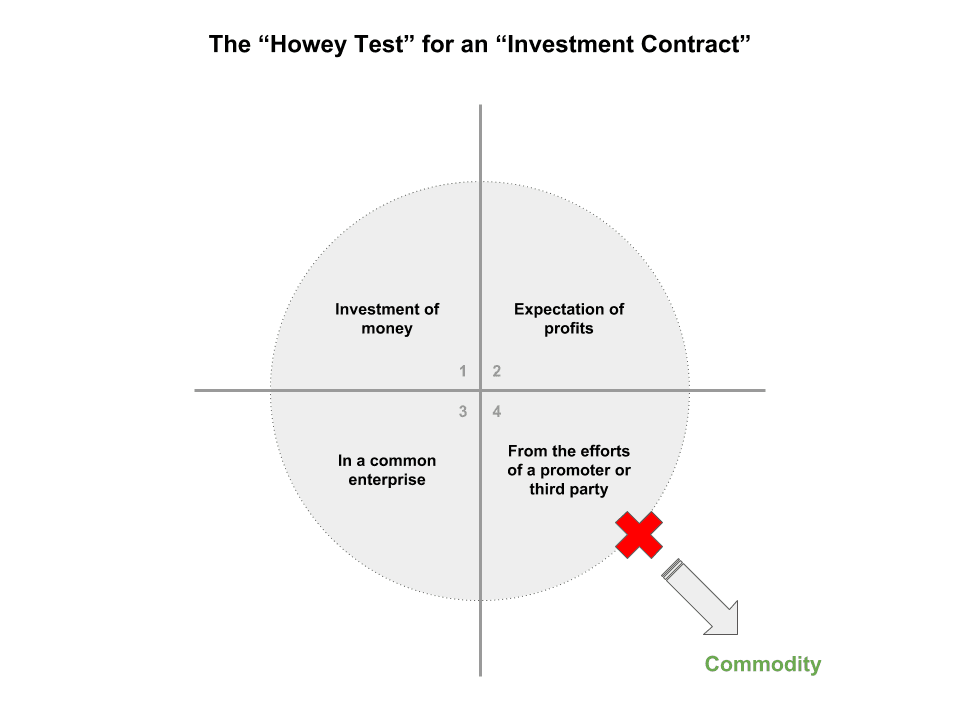
First: the what constitutes a “security” has been defined by the courts more specifically as an “investment contract”, which is a transaction with the following properties:
- An investment of money
- With the expectation of profits
- In a so-called “common enterprise” (roughly meaning: investors and the company rise and fall together)
- From the efforts of a promoter or third party (some dispute over whether this means “solely” from a promoter, but clear that it entails “significant managerial efforts” of a single promoter)
This four-part test was established as part of SEC vs. Howey, a 1946 supreme court case involving the sale of tracts in an orange grove, with an associated lease-back arrangement where buyers of the land leased the land back to the Howey corporation in exchange for profits generated from cultivation of orange crops. This so-called “Howey Test” is now the basis for determining whether such a transaction constitutes an “investment contract” and would therefore fall under securities laws (with all associated registration and disclosure requirements).
The way the test works is that, if the contract satisfies all 4 “prongs”, it “passes” the Howey Test and is therefore a securities transaction. If the contract does not satisfy any one of the prongs, it fails the Howey Test and is therefore is not a securities transaction.
The 4 prongs of the Howey Test
Ok, with all of that as background, here is how I see the Howey Test — 4 prongs that all need to be satisfied:
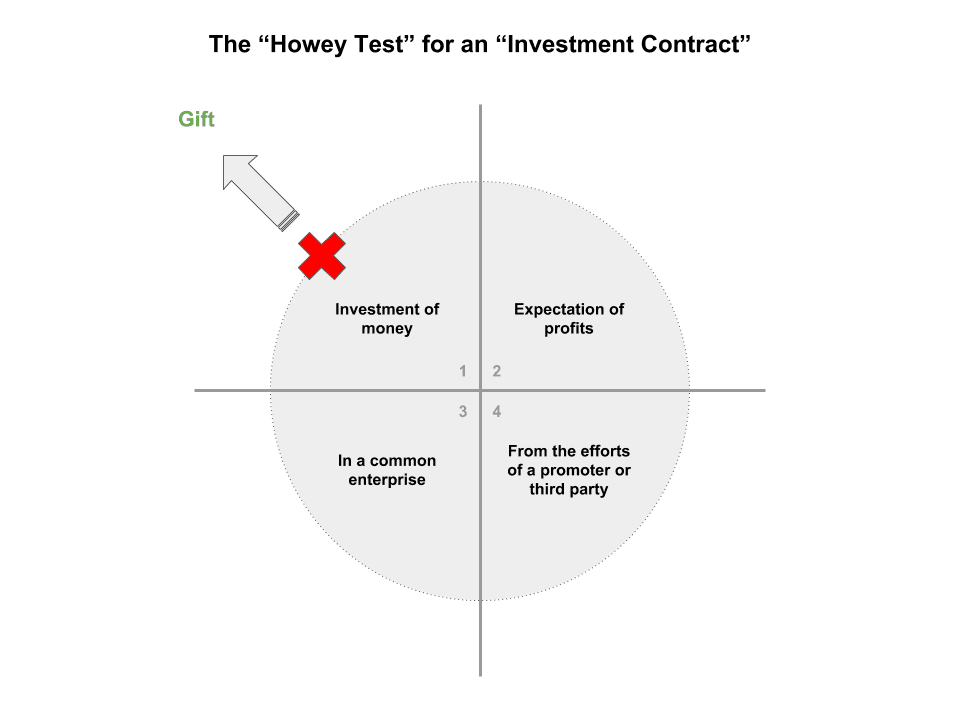
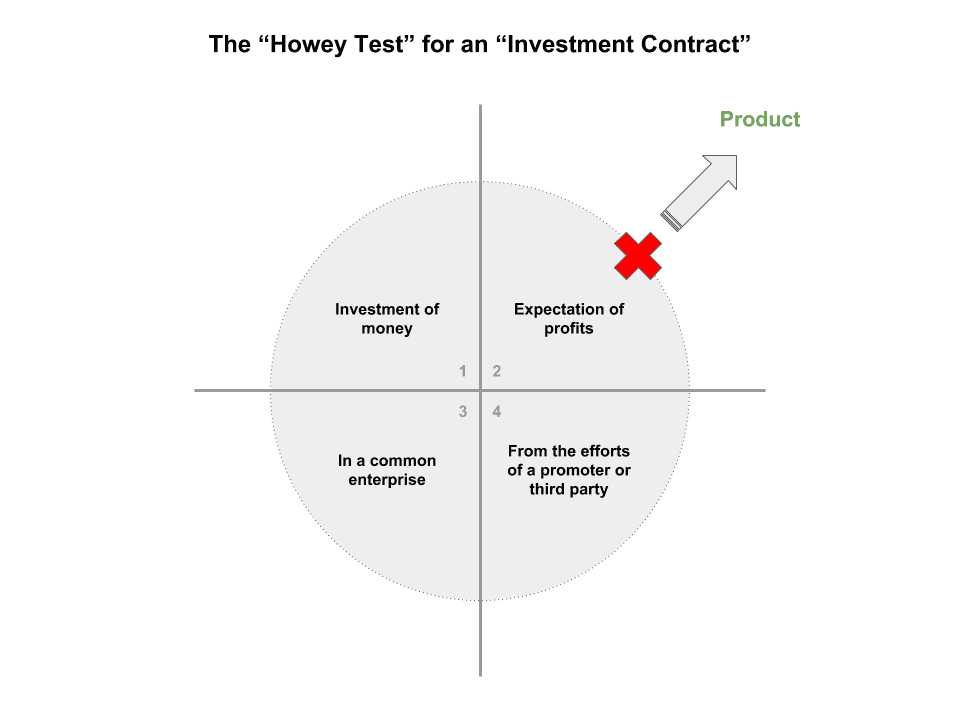
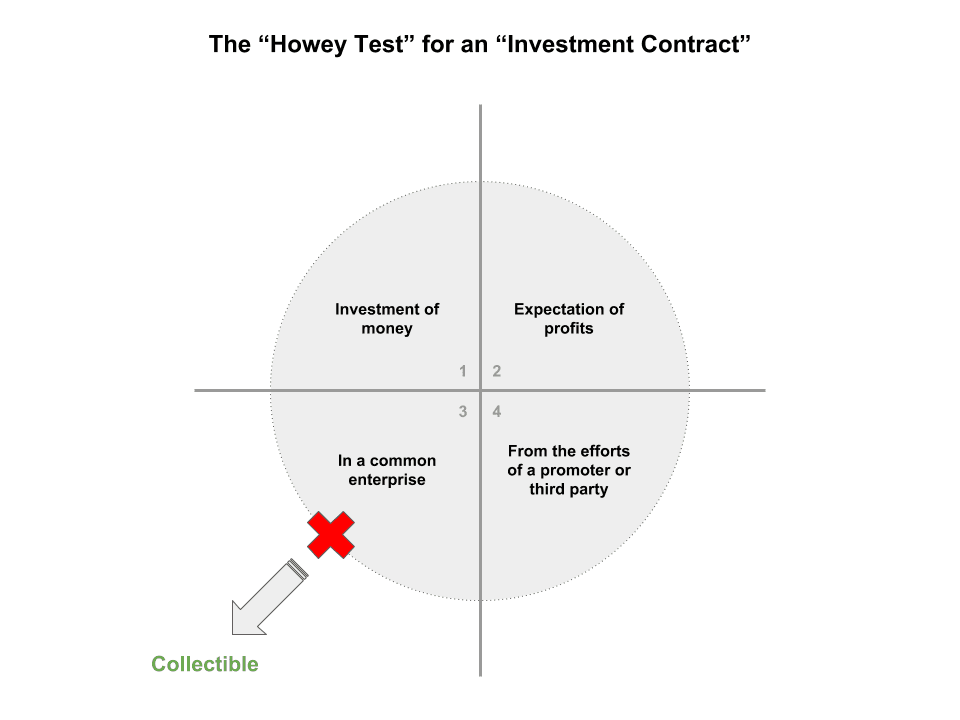
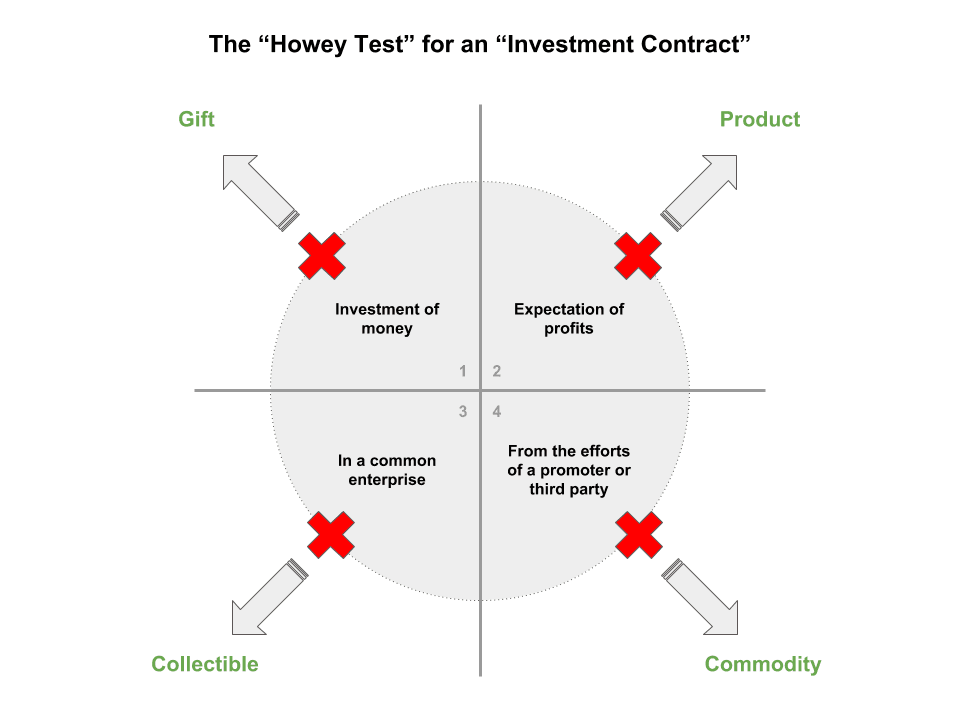
So, if you were to start to think about how to “knock out” prongs of the test, thereby removing a transaction from securities status, you’d start one-by-one.
1) Remove the “investment of money” and what you have looks more like a Gift (think: receiving airline miles, or ride credits on Uber, or “airdrops” of tokens in a crypto network)
2) Remove the “expectation of profit” and what you have looks more like a product (think: pre-buying a backpack or movie on Kickstarter, purchasing laundry or arcade tokens, or buying Stacks Tokens to insert records in the Blockstack blockchain):
3) Remove the “common enterprise” and what you get looks more like a collectible (think unique items like stamps, baseball cards, or CryptoKitties):
4) Finally, remove the “efforts of a promoter or third party” and what you get looks more like a commodity (think gold, wheat, or Bitcoin or Ethereum):
All together, it looks like this:
Is a “security” an asset or a transaction?
A key question throughout all of this is whether the “security” is the digital asset itself, or instead the transaction involving the digital asset.
In a key speech by the head of SEC’s Corporate Finance Division, Bill Hinman, earlier this year, he addressed this question head on:
To start, we should frame the question differently and focus not on the digital asset itself, but on the circumstances surrounding the digital asset and the manner in which it is sold. To that end, a better line of inquiry is: “Can a digital asset that was originally offered in a securities offering ever be later sold in a manner that does not constitute an offering of a security?” In cases where the digital asset represents a set of rights that gives the holder a financial interest in an enterprise, the answer is likely “no.” In these cases, calling the transaction an initial coin offering, or “ICO,” or a sale of a “token,” will not take it out of the purview of the U.S. securities laws.
But what about cases where there is no longer any central enterprise being invested in or where the digital asset is sold only to be used to purchase a good or service available through the network on which it was created? I believe in these cases the answer is a qualified “yes.”
The Hinman speech clarified two things: 1) that by knocking out the “efforts of others” prong of the Howey Test (#4 above) a crypto asset transaction can be viewed through the lens of commodities vs securities and 2) that an early transaction of that asset (in this case the pre-sale of ETH) can be analyzed under Howey distinctly from a later sale, given different facts and circumstances at the time.
This last part is really important, and I still have a hard time pinning down (really smart, expensive) lawyers on the subject. There is an idea that a “security” is a thing rather than a transaction, which does seem at odds with both Howey and the Hinman speech. In the case of Howey, the oranges produced under the contract are not the same as the contract itself (similar to contracts for future tokens), and in the case of the Hinman speech, it’s the transaction rather than the underlying token (BTC or ETH).
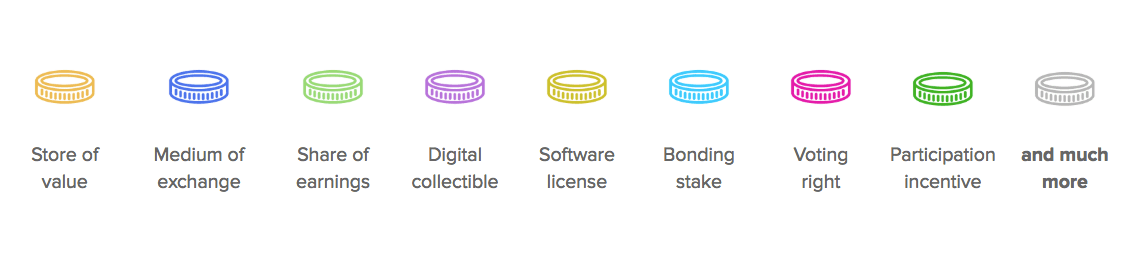
Finally taking all of this together, it’s important to remember that 1) there are many kinds of cryptoassets, and 2) they are offered/sold/traded/transferred under different circumstances over time. I think about it like this:
I hope that is helpful. This is complicated stuff, and new territory.

